
Ethical Hacking: A Hands-on Introduction to Breaking In
Understand how systems are attacked from a hacker’s perspective. Acquire the foundations of Ethical Hacking and fortify your networks for a safer, more connected future
Ethical Hacking: A Hands-on Introduction to Breaking In
An 8-week course with expert-led sessions, real-life project and teamwork
This course offers a comprehensive journey into the world of ethical hacking for students interested in cybersecurity and network protection. It elucidates the principles governing the identification, exploitation, and prevention of network vulnerabilities, with ample hands-on opportunities to apply these principles in a secure, simulated environment. The skills and knowledge gained from this course form the bedrock for understanding and implementing cybersecurity measures across various digital platforms, thereby building a strong foundation for further learning in cybersecurity and network defense. Linking theory to practical application and real-world scenarios is a major theme of the course. Furthermore, this course will consistently refer to applications in areas of key interest such as corporate networking, cryptography, and social engineering. By engaging with this course, students will gain not only a theoretical understanding of ethical hacking but also the practical skills needed to help secure a network environment, hence fulfilling their crucial role in the world of digital security.
Program Structure
Typical week in the cohort
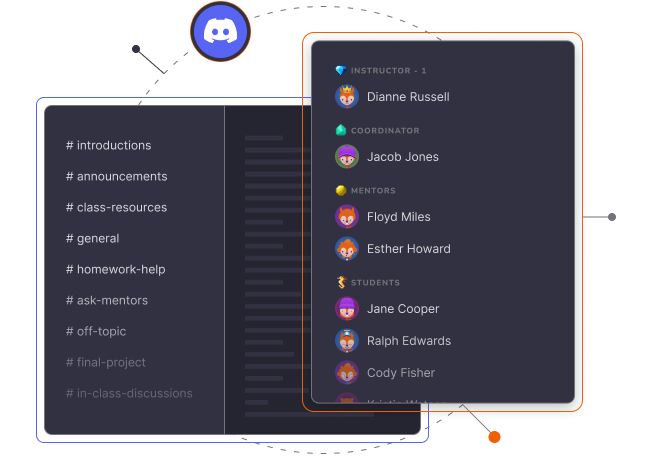
Communication and networking are core components of the ClasspertX course experience. In this course, you will be part of a global learning community. In order to accommodate all participants, we have designed much of the course experience to take place asynchronously, with a synchronous class session that occurs weekly.
-
Reading from the book
 Includes a free copy of the book
Includes a free copy of the bookThis course is centered around Ethical Hacking: A Hands-on Introduction to Breaking In which will be used as a supplementary material for the classes
- Videos
- Quizzes
- Exercises
- Students will be prompted to submit questions during the week, and the instructor should choose questions to answer for students during the weekly session
 Sync Sessions on Zoom
Sync Sessions on Zoom- Q&A with the instructor
- Additional demos / examples of key topics
- Group practice - students break out to work on an exercise
- Group discussion
Syllabus
- Understand what the course will cover
- Understand what is expected of participants in this course
- Understand how to get the most out of this course
- Meet your instructor
- Understand how internet scanners work
- Perform basic scans with shodan and netlas.io
- Perform advanced scans
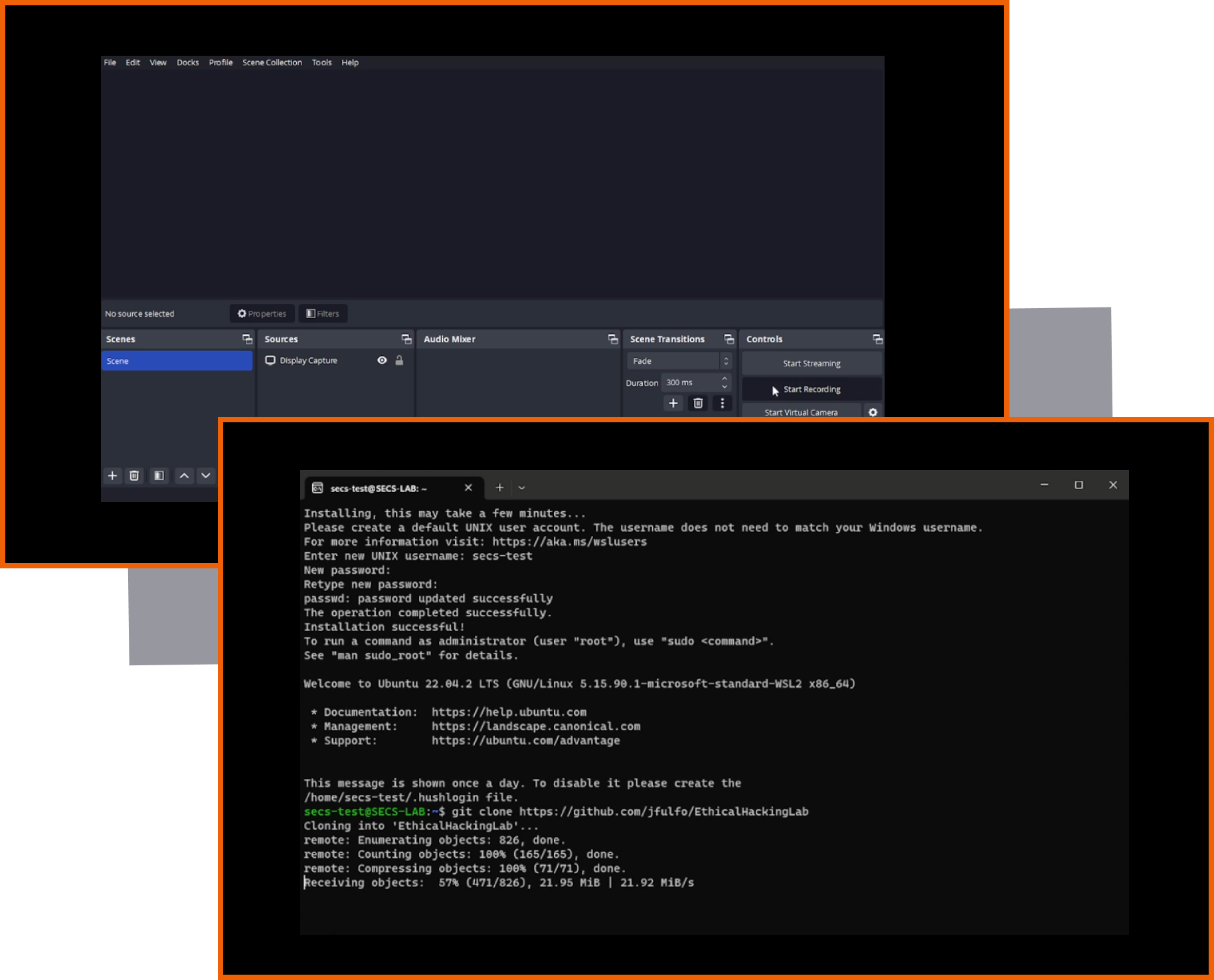
- Terraform and Virtual Machines
- Azure Cloud Computing
- Setup a cloud pentesting lab that they can practice their skills
- Understand the fundamentals of how these scanning tools work
- Difference between active and passive scanning
- Enumerate a netwrok using a variety of scanning tools
- Manual exploitation techniques (searchsploit)
- Manual privilege escalation techniques (SUID, etc)
- Manual persistence techniques (Cron jobs, Windows registry)
- Scan target with Metasploit
- Set a metasploit module and exploit a target
- Escalate privileges and establish persistence on target
- Metasploit framework's general architecture
- Write a basic Metasploit module
- Examples of more advanced modules
- Understand the fundamentals of symmetric key cryptography
- Understand the fundamentals of asymmetric key cryptography
- Write custom ransomware that use both symmetric and asymmetric cryptography
- Develop a complete plan of attack from scanning to establishing persistence
- Execute this attack in the cloud lab environment
- Learn a variety of techniques for evading anti-virus systems
What you'll learn
- Understand the fundamentals of networking and different types of network attacks
- Learn how to set up a virtual lab environment for ethical hacking
- Gain knowledge about various tools and techniques for exploiting network vulnerabilities
- Understand how encryption algorithms secure digital communications
- Learn the concept of social engineering and how to use it for ethical hacking
- Understand the common patterns in vulnerability exploitation and learn how to identify and exploit them.
- Learn how to control networks, escalate privileges and move through corporate networks
- Develop Python programming skills to build your own tools for ethical hacking
- Understand the ethical considerations and best practices in hacking to ensure you're acting responsibly and legally
Who this course is for
The skills and knowledge gained from this course form the bedrock for understanding and implementing cybersecurity measures across various digital platforms, thereby building a strong foundation for further learning in cybersecurity and network defense

Who this course is for
Target Audience- Students with a computer science or sys admin background who want to understand how attackers break into systems, so that they can defend these systems more efficiently
- Aspiring ethical hackers who want to work as freelance security consultants or within organizations to find and fix security issues
- Cybersecurity enthusiasts and bounty hunters
- No prior experience with Ethical Hacking or Cybersecurity
- Knowing how to program is necessary
- Experience with Linux and the Linux command line is a plus
- Understanding of networking concepts is a plus
Your Instructors

Daniel G. Graham is an accomplished author and researcher with a keen interest in secure embedded systems and networks. Recently, he authored two books, “Ethical Hacking” and “Metasploit 2nd.” Before transitioning to teaching, Dr. Graham previously worked as a Program Manager at Microsoft in Seattle, Washington. His work has been published in IEEE journals relating to sensors and networks. He has taught several courses, including JavaScript, React Native, Computer Networks, and Software Engineering
- Author of both "Ethical Hacking" and "Metasploit: The Penetration Tester's Guide"
- Assitant Professor at University of Virginia
- Ph.D at William & Mary
- Program Manager at Microsoft
Another Great book from the No Starch Press, for geeks like me, it is no surprise that it stands up to my expectations. It is good for starters that will take you to the intermediatory level in the field of Ethical hacking
Great book so far. 5/5 for me. Well written, lots of great, solid information that is up to date, great explanations, and even labs to go with it! I haven’t finished just yet, but i have gone through enough to write a review. great stuff! EDIT: I am also a beginner in this field, if that helps :)
First, I bought this book (and paid the full price) from a local bookstore. Also, I have not finished the entire book yet, but so far I am having a lot of fun learning.
If you don’t have any computer or network experience, the learning curve on this subject will be amazingly steep. It starts with relatively simple concepts but jumps quickly into the heart of networking. Anyone can follow along, but understanding it well enough to know what or why could be difficult. The title of the book might be enough to tell you that. The hands on examples given may not work on all systems and you may have to make some changes. Experience with IT concepts will help you stay on track. For example, not all ISP provided equipment works the same and you may need to make changes to your home network, or you may run into issues with outdated libraries in Linux preventing a Python script from running. Knowing what to do will save you a lot of time.
If you have some background in IT, like Help Desk or network engineering experience, this will be a fun journey into Ethical Hacking. You’ll need a computer powerful enough to host about 5 Virtual Machines, but if you are in the computer section of a bookstore looking at Ethical Hacking topics, you probably already have this.
Frequently Asked Questions
-
Can I get my employer to pay for the program?
An investment in knowledge always pays the best return for your company. It’s a tiny investment compared to what you could potentially bring in terms of innovation to your workplace.
Many companies offer reimbursement for courses related to your job. Ask your employer about tuition benefits. Even if there is no specific tuition assistance, many companies allocate money toward professional development. Managers may have money earmarked for industry conferences and many have not considered applying it toward continuing education.
Approach asking for tuition assistance like you would a formal negotiation. Go into the discussion with clearly outlined and rehearsed messages about what you hope to gain and emphasize how it will benefit your boss and organization.
-
What is the time commitment for this course?
This course requires 6-8 hours/week of work. Self-paced activities such as homework assignments, readings, and watching video lectures exist to help you build up knowledge until you’re able to demonstrate, through your project, that you’ve achieved the learning outcomes of the program. Although important, homework assignments won’t be graded by the instructional team. The only gradable unit in this program will be your project, which is a prerequisite for certificate emission
-
How do refunds work?
If the course does not meet your expectations, you can ask for a full refund before the beginning of week 3. No questions asked!
-
How are certificates issued? Will I be evaluated?
In order to earn a certificate, you’ll need to submit a project and get a passing grade. The instructional team will provide comprehensive feedback on your project, highlighting the strong points, areas for improvement, and helpful tips on how it could be successful outside of the class.
-
Will this course run again in the future?
Cohort-style classes are to some extent very similar to traditional classroom environments which makes them largely dependent on the instructor’s schedule. While we always hope there’ll be a next cohort, there’s no guarantee that the instructor will be available for the next one. If you’re busy right now, but really interested in taking this course, we advise you to sign up now and ask for a refund if you can’t commit to the program after week 3.
-
What determines the price of the course?
Our programs require significant time from a number of professionals including mentors, the instructor, and organization staff. It is not a canned lecture course but an educational opportunity tailored to your needs and interests.
Ready to level-up?
Enroll now in one of our programs
and join us for a truly immersive learning experience
Measure and apply statistics to evaluate an artifact or its function

Create a Game Design Document and Pitch the Concept to Industry Experts


Flint Dille, John Zuur PlattenWriters of Jurassic World, Diablo, Transformers and more

Build a Programming Language from the Ground-Up


Uncover Vulnerable Machines and Launch an Effective Attack with Your Self-Made Ransomware

Design and Build a System that Solves a Problem You Find Interesting

Create a Professional-Looking Object from Conception to Reality


Build a Multi-Level Car Parking System Using Pointers in C/C++


Build a Blockchain Application and Pitch it to Real Investors

Develop and Manage a Successful AI Project for your Organization

